Fast Linux software KVM with clipboard sharing.
Nikau accesses devices through Linux uinput APIs. Events are sent over UDP using the low-latency QUIC protocol. Any Linux machine should work, including Wayland, X11, and even Linux consoles. Keyboards, mice, and touchpads are all tested and supported, other device types should work as-is. OSX and Windows are not currently supported.
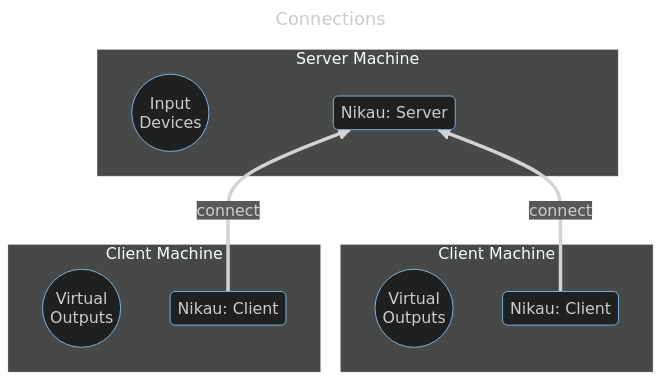
Nikau is packaged as a single standalone executable containing server and client modes. The server is where the input devices are plugged in. Clients running on other machines then connect to the server and wait to receive input events.
The Nikau server has configurable keyboard shortcuts for switching among connected clients. The defaults are LeftAlt+N to go to the next machine and LeftAlt+P to go to the previous machine. Another option is to send SIGUSR1 and SIGUSR2 unix signals to the Nikau server process.
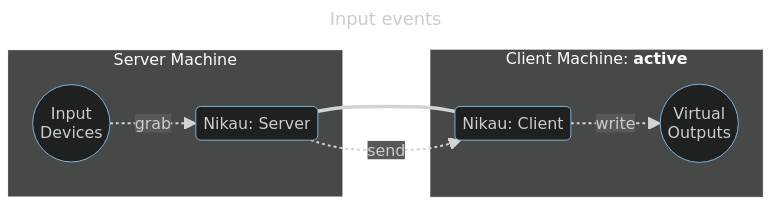
When a client has been selected to receive input, the Nikau server collects input device events from the host and sends them over the network to the selected client. That client then emits the received input events to the host.
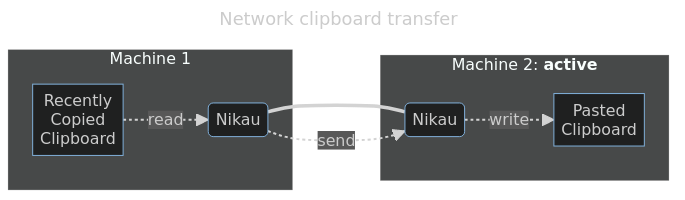
When Nikau is started from within a WM, clipboard contents can be automatically transferred between machines over the network. This transfer happens automatically in the background when the user creates a clipboard entry on one machine, switches to another machine, and then pastes to that machine. Server-to-client, client-to-server, and client-to-client transfers are all supported. Any content is supported, up to a configurable 5MB size limit.
cargo install nikau, and then use sudo ~/.cargo/bin/nikau to run the binary.main: git clone https://git.sr.ht/~nickbp/nikau && cd nikau, then use ./server.sh and ./client.sh <server-host> helper scripts.docker-server.sh and docker-client.sh provide example docker run commands. Note that --privileged is required and this has security implications. Image tags are based on commit SHAs and are listed here.nikau binary on each machine:
sudo nikau server on your server machine with the input devices to be sharedsudo nikau client <serverIP> on your client machine(s)New connections need to be approved on both the server and the client. On each side of the connection, check that the displayed fingerprint matches what's printed on the other side. This manual approval is only required the first time a new connection is being made. Approved peer certificates are written to ~/.config/nikau/known_certs/<fingerprint>.pem and can be revoked by deleting them.
Once the connection has been made, the client is added to the server's rotation. Keyboard shortcuts and signals are used to switch among the server and one or more clients.
LeftAlt+N and LeftAlt+P shortcuts to switch forward and backward among a rotation of connected clients (in order of client IP) and the server itself. These shortcuts can be customized to use a different keyboard combination. Forward and backward rotation can also be triggered by sending SIGUSR1 and SIGUSR2 unix signals to the Nikau server process like this: sudo kill -USR1 <pid>LeftAlt+1 could be switch to a client whose fingerprint starts with abcd123LeftAlt+2 for switching to another client whose fingerprint starts with efgh456LeftAlt+0 could switch to the server (empty fingerprint)--shortcut-goto leftalt,1=abcd123 --shortcut-goto leftalt,2=efgh456 --shortcut-goto leftalt,0=
Keyboard shortcuts are configurable via commandline arguments on the Nikau server. For a full list of supported key names, see the list of KEY_* entries here. For example leftshift,rightctrl,x would be mapped to the KEY_LEFTSHIFT, KEY_RIGHTCTRL, and KEY_X keys on that list.
I'm regularly using Nikau across a variety of machines and devices, making fixes and improvements as needed. As such it should "just work". Feel free to email me if you encounter problems.
Keyboards, mice, and touchpads should all be supported and are used regularly. Other input devices like joysticks, gamepads, tablets, etc should also work, but I haven't tried them yet. To maximize device compatibility, Nikau passes device events largely as-is, so most devices should Just Work.
The client/server protocol may change between releases. The server should automatically detect and refuse clients with incompatible versions. If you see version errors upon connection, check that the versions line up using nikau --version. Compare this to the latest stable release. Upgrade by running cargo install nikau again.
Known shortcomings:
--max-clipboard-size-kb argument on all machines. Some Wayland compositors may lack support for either ext-data-control or wlr-data-control extensions, but this can be fixed by using a better compositor.This software has NOT undergone any security review or audit. Use is at your own risk. See also terms and conditions of the licence.
Nikau's purpose is to collect keystrokes and clipboards and send them over the network between machines. This can include passwords and other sensitive information. You must decide whether this is an acceptable risk for you.
Assuming no flagrant bugs in Nikau or its dependencies, all communication is TLS-encrypted, with certificate-based authentication following a "prompt-once" model similar to OpenSSH. New connections must be approved bidirectionally, on both the client and the server, before the connection can proceed. However, even with encrypted channels, timing information could still be inferred from the event stream.
In order to allow direct access to uinput devices, the client and server must both be run as root (e.g. via sudo).
There are a few other packages for this sort of thing. Here's how Nikau compares, in my highly biased opinion:
This project is licensed under the AGPLv3 (or later versions) and is copyright Nicholas Parker.